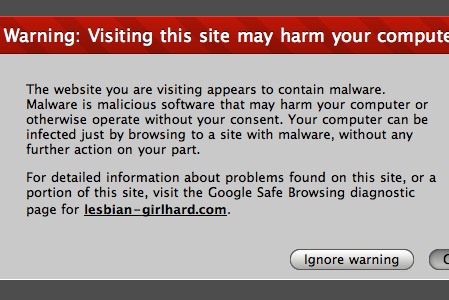
Westminster Ingleside King Farm Presbyterian Retirement Communities has experienced a malware infection that may have resulted in the attackers obtainingt he protected health information of may of it patients.
The assisted living facility, based in Washington D.C., had put in place a wide variety of security solutions to block unauthorized access to its IT systems, although in this instance they were unable to obstruct the malware attack.
The malware was first noticed on November 21, 2017, with swift action taken to identify every piece of the malware on its network and eradicate the malicious code to prevent further attacks. While the malware was properly deleted, a third part company was hired to examine how the attackers had managed to bypass the security measures in place, and whether access to the protected health information of its residents had happened.
The internal inquiry into the breach emphasized many areas where security could be improved to further strengthen its systems from malware attack. Ingleside has now established a new firewall, upgraded its anti-malware and antivirus software, and has adopted two-factor authentication on user accounts. New user credentials have been set up and stronger passwords implemented. Workers have also had more security training to help them spot unauthorized access.
While nothing has been found during the review to suggest the protected health information of its residents was accessed, data access and data theft could not be 100% ruled out. As a result, all those potentially affected have been notified about the potential breach and, as a precautionary measure, patients have been offered credit monitoring and identity theft protection services via Kroll for free for the next year.
There was no exposure of financial information due to the malware infection, although names, addresses, Social Security numbers, and other protected health information were potentially downloaded.
The breach notice, required as per HIPAA legislation, submitted to the Department of Health and Human Services’ Office for Civil Rights (OCR) indicates up to 5,228 residents were hit by the malware attack.