HIPAA Data Breach Statistics
HIPAA data breach statistics are useful for understanding the threats to protected health information (PHI) in the healthcare industry. In 2009, the HITECH Act made significant changes to how HIPAA is applied and enforced. One of the changes – the Breach Notification Rule – requires Covered Entities to notify affected individuals and HHS´ Office for Civil Rights when a breach of unsecured Protected Health Information (PHI) occurs.
When a breach affecting more than 500 individuals is notified to HHS´ Office for Civil Rights, the HITECH Act requires the agency to publish details of the breach via an online Breach Report. It is from the Breach Report and its archive that our HIPAA data breach statistics have been extracted.
The Causes of HIPAA Data Breaches
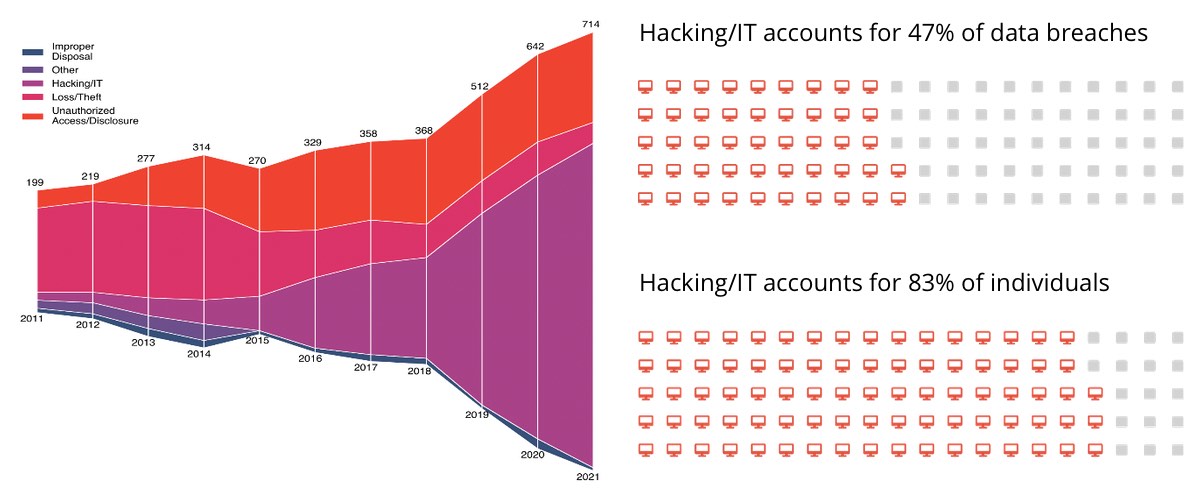
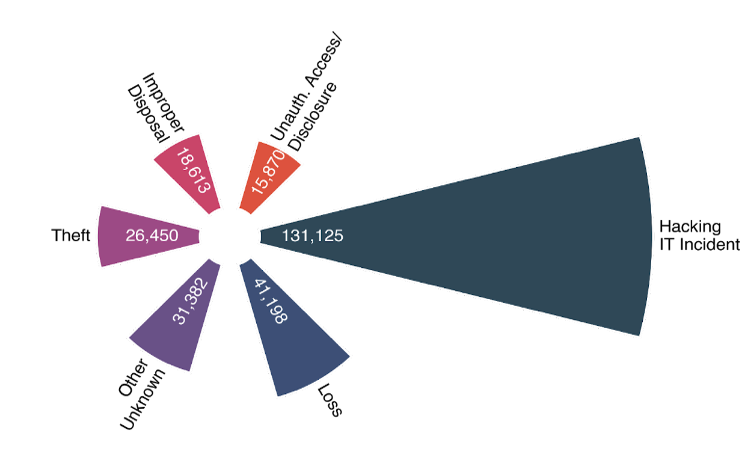
In the early days of the Breach Report, the majority of HIPAA data breaches were attributable to the loss or theft of devices and media, or unauthorized access to – or disclosure of – PHI. However, due to HITECH´s Meaningful Use program and the incentivized digitalization of PHI, there has been a significant increase in HIPAA data breaches attributable to hacking and IT security events.
The image below indicates how quickly the number of HIPAA data breaches attributable to hacking and IT security incidents has grown since 2015. Hacking and IT security incidents now account for 47% of all data breaches notified to HHS´ Office for Civil Rights since the passage of the HITECH Act, and – significantly – account for 83% of all affected individuals.
There are two important caveats in these statistics. The first is that the “Hacking/IT Security” category is often interpreted as breaches attributable to external bad actors. Although many data breaches are due to external bad actor acquiring unsecured PHI via malware, phishing, or ransomware, a significant number are due to misconfigured servers failing to secure PHI.
The second caveat is that, when a Covered Entity notifies HHS´ Office for Civil Rights of a data breach, it has to assign a category to the breach. Consequently, a data breach could involve multiple categories, but because the final event – or the event due to which the breach was discovered – was a Hacking/IT Security incident, the breach is assigned to this category rather than any other.
For example:
- A Covered Entity fails to provide security and awareness training to all members of the workforce (Other) >
- Due to the lack of security awareness training, an employee falls for a phishing email (Loss/Theft of login credentials) >
- The stolen login credentials enable an external bad actor to access databases containing PHI (Unauthorized Access) >
- The external bad actor extracts the PHI to monetize on the black market (Hacking/IT Security incident).
The Size of HIPAA Data Breaches
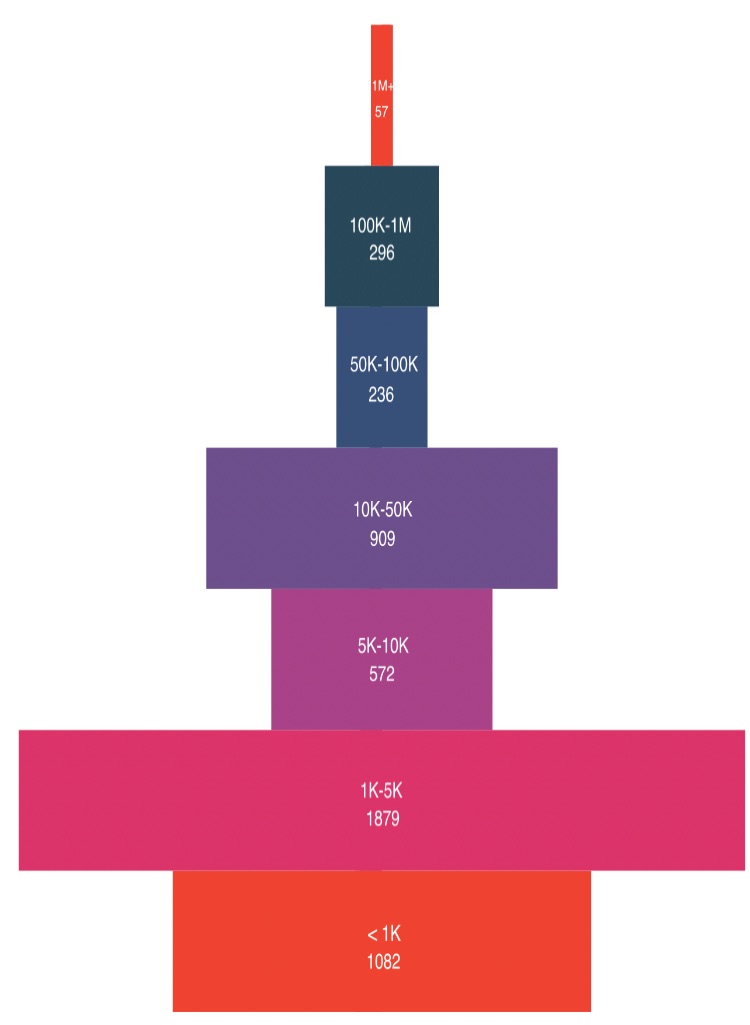
Although the number of data breaches is increasing, the average size of data breaches in terms of the number of individuals affected has remained fairly constant year-on-year – excepting 2015 when the Anthem breach (78.8 million individuals affected), the Premera Blue Cross breach (11 million individuals) and the Excellus breach (10 million individuals) were reported in the same year.
Since 2011, there have been six years in which the average size of a data breach has been 50,000 individuals or fewer – the most recent occurring in 2020. As the image below indicates, the majority of data breaches affect fewer than 5,000 individuals, and the percentage of “small” data breaches would be even greater if HHS reported on data breaches affecting fewer than 500 individuals.
Average Size of Breach per Cause
Such was the case in 2016, when Newkirk Products Inc was the victim of a Hacking/IT Security incident which affected 3.3 million individuals. Newkirk Products Inc. provided a Business Associate service to thirteen Covered Entities; so rather than HHS receiving thirteen notifications with an average breach size of 250,800 individuals, the thirteen incidents were consolidated into one.
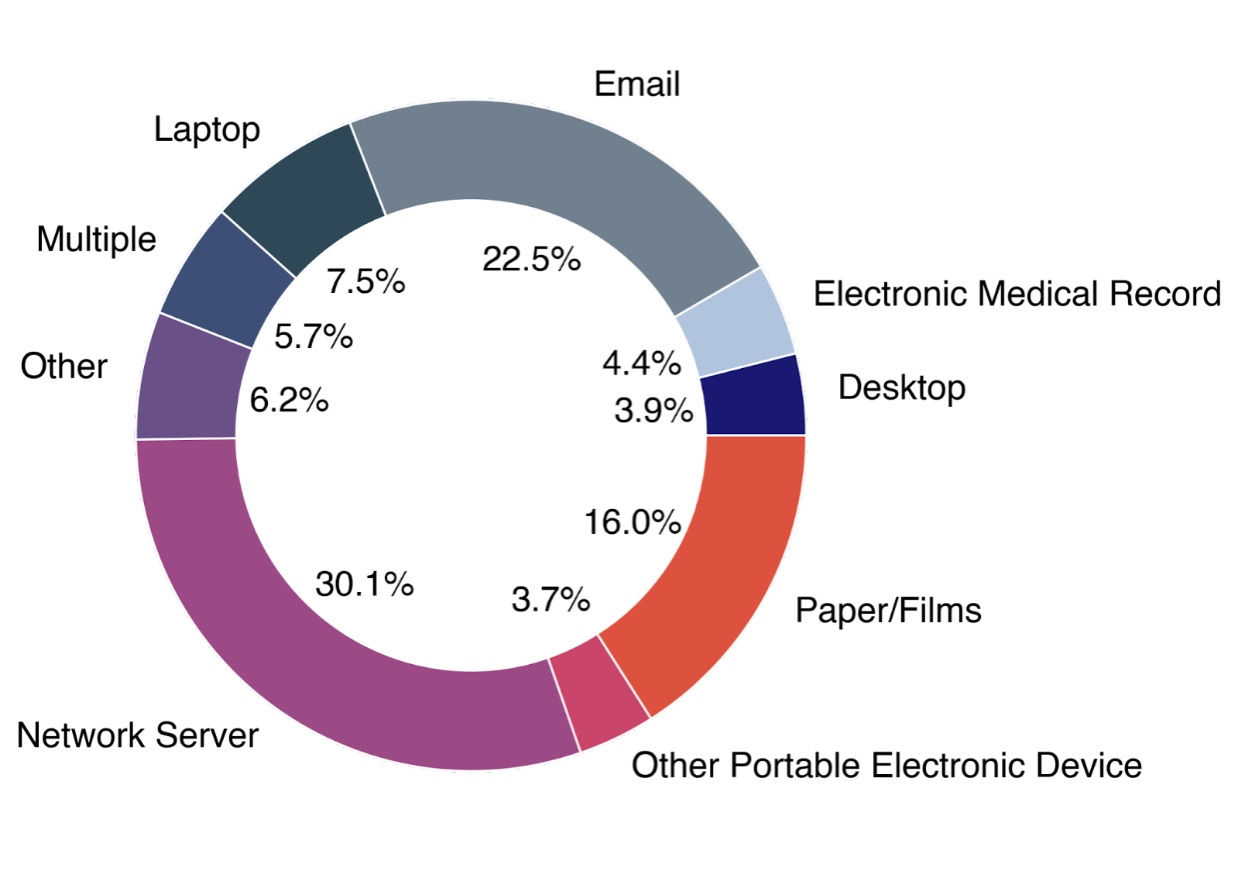
How Each Data Breach Occurred
In the archive section of the Breach Report, it is possible to view a “web description” of each breach which explains how it occurred. It can be worthwhile reading the web descriptions inasmuch as they reveal many different ways in which data can be breached, and this can help Security Officers identify gaps in their risk assessments if a breach has occurred for a reason they had not considered.
One observation in the descriptions of data breaches is the number attributable to a Business Associate experiencing a ransomware attack. This implies a large proportion of Business Associates do not have the necessary safeguards/procedures/training to limit the threat of ransomware to a reasonable and appropriate level. However, it is also important to be aware that all ransomware attacks are notifiable events unless a low probability of compromise can be demonstrated.
Consequently, if a ransomware attack occurs, and a Covered Entity or Business Associate responds to it by isolating the infected systems, cleansing them, and restoring data from a malware-free backup, the attack is notifiable – even though no data may have been lost or compromised – because, at the time of the ransomware attack, the data maintained in the compromised systems was under somebody else´s control and unavailable to the Covered Entity or Business Associate.
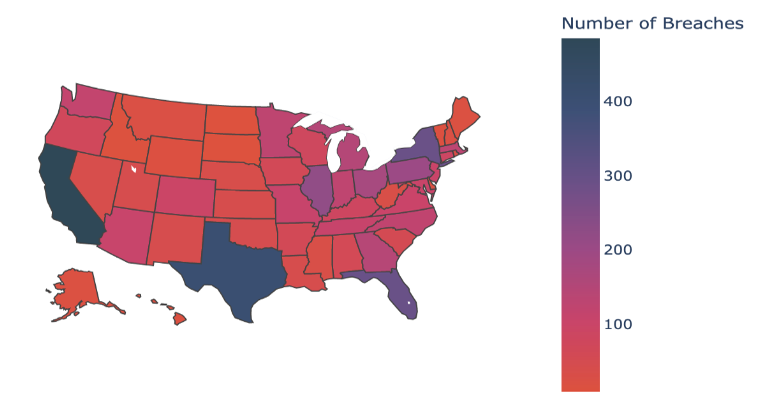
Where Data Breaches Occur Geographically
It is no surprise that the states with the highest number of data breaches recorded on the Breach Report are those with the highest populations – California, Texas, Florida, and New York. However, the proportion of data breaches per state rarely aligns with the proportion of individuals per state across the country. For example, 3.5% of data breaches are reported from organizations in Massachusetts, yet the state only accounts for 2% of the total population.
It is not necessarily the case that a higher proportion of data breaches occur in Massachusetts. Since 2010, all businesses in the Bay State have had to comply with strict data security laws which include a breach notification provision. Although the HIPAA Breach Notification Rule has been effective since 2009, it is likely the case that there is a greater awareness of notifying data breaches in Massachusetts than in some states without such comprehensive notification regulations.
Fines for HIPAA Data Breaches
HHS´ Office for Civil Rights does not often issue fines for data breaches – the agency preferring to resolve violations of HIPAA via Corrective Action Plans. However, Corrective Action Plans are not “cost-free” as they often involve the development of new policies, the implementation of security safeguards, and the provision of training to ensure members of the workforce are aware of the new policies and security safeguards. The cost in terms of business disruption can be substantial.

In some cases, a civil monetary penalty for violating HIPAA may only be one of many financial penalties. For example, Anthem Inc. not only settled with HHS´ Office for Civil Rights for $16 million, but also settled two State Attorneys General investigations for a total of $48.2 million, and a consolidated class action lawsuit for a further $115 million.
Raise the level of HIPAA Awareness in your organization with Learner-Friendly, Comprehensive and Affordable HIPAA Training.
COMPREHENSIVE HIPAA TRAINING
Used in 1000+ Healthcare Organizations and 100+ Universities