Hancock Health , based in Greenfield, Indiana experienced a ransomware attack on Thursday last week.
Employees of Hancock were forced to use offline methods to record patient health information, while IT staff tried to respond to the attack and save the encrypted files.
The attack kicked off at began around 9.30pm on Thursday night when files on its network were hit with encryption. The attack initially caused the network to operate slowly, with ransom notes being being visible on screens showing files had been encrypted. The IT team moved swiftly and started shutting down the network to restrict the success of the attack and a third-party IT firm was hired to help react to the ransomeware attack.
Operations continued as normal during the attack according to Hancock Health.
The results of an investigation into the attack uncovered nothing to suggest any patient health information was obtained by the attacker(s). The target of the attack was solely to cause disruption and lock files so the hospital would have to pay a ransom to recover its files.
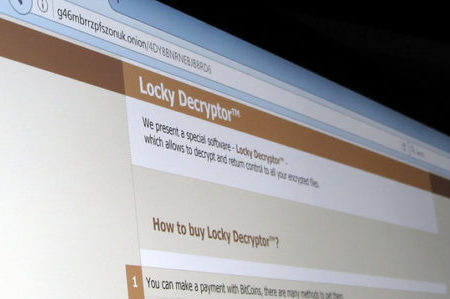
An article published in the Greenfield Reporter stated that the attack involved a variant of ransomware called SamSam. The ransomware variant has been seen in numerous attacks on healthcare companies in the USA over the past 12 months. The unknown attacker(s) requested a payment of 4 Bitcoin to purschase the keys to remove the encryption from the network.
In line with HIPAA regulations, Hancock Health had performed backups and no data would have been lost following the attack; however, the process of recovering files from backups takes a major amount of time. The hospital would not have had access to files and information systems for some time if backups were used to restore the data. On Saturday, steps taken to pay the ransom.
The decision to pay the ransom was only taken after a lot of consideration. While patient services were not harmed, restoring files from backups would almost definitely have harmed patients and paying the ransom agreed to be the best option to avoid any disruption. The keys to remove the encryption were handed over within two hours of the ransom being paid and the network was brought back into operation on Sunday.
In most cases, these attacks are incurred when employees respond to phishing emails or visiting malicious websites online, although Hancock Health says this attack was not the result of employee being fooled by a phishing email.
Hancock Health has now added software that can detect unusual network activity that suggests an intrusion or ransomware attack, which will permit measure to be taken quickly to block, and limit the extent, of any additional attacks.