A hacker has potentially gained access to the medical records of up to 24,000 patients of Decatur County General Hospital in Tennessee. Teh Helath centre has discovered malware has been placed on a server storing its internal electronic medical record system.
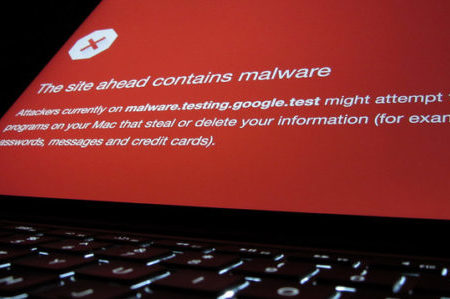
A abnormal software installation was found on November 27, 2017 by the hospital’s medical record system supllier, which is used to maintain the server on which the system is stored. A review showed the software was a type of malware referred to as a cryptocurrency miner.
Crytptocurrency mining refer to using computer processors to verify cryptocurrency transactions and add them to the public ledger storing details of all transactions since the currency was established. The procedure for verifying transactions requires computers to solve complex computational equations.
Cryptocurrency mining can be carried out by anyone with a computer, and in return for solving those computational equations, the miner is given a small payment for verifying the transaction.
A computer, operating on its own, can be used to earn a few dollars a day carrying out cryptocurrency mining. Large amounts of computers can generate reasonable profits. A group of cryptocurrency mining slave computers, such as those infected with cryptocurrency mining malware, can lead to substantial earnings. Cryptocurrency malware campaigns and infections have grown in recent months.
Since cryptocurrency mining needs a considerable amount of processing power, computers infected with the malware may run more slowly, although it may not always be obvious that infection has happened. In the instance of Decatur County General Hospital, the malware infection was not found by its EMR vendor for over two months. The malware is thought to have been placed on the system on or before September 22, 2017.
Cryptocurrency mining malware normally only has one role. The malware is not normally paired with data theft. However, on this occasion, the attacker is thought to have gained access to the server in order to upload the malware. Access to patient data was able to be gained due to this.
Decatur County General Hospital completed an in-depth review into the server breach and malware infection, and while no proof of data access or data theft was found, it was not possible to reasonably verify that data access had not happened. Therefore, the decision was taken to send out notifications to patients that protected health information had potentially been obtained.
Due to the sensitive nature of data held on the server – names, addresses, birth dates, Social Security numbers, diagnoses, treatment details, and insurance billing data – all patients affected by the incident have been offered credit monitoring services for 12 months through True Identity without charge as a precautionary measure.
No proof of misuse of patient data has been reported to date and the hospital feels the sole purpose of the attacker was to upload the malware, not to obtain patient data. However, patients have been told to exercise caution and monitor their accounts, credit, and EoB statements for any proof of fraudulent activity and to be cautious of any communications received over the the telephone, mail, or email regarding the incident.