In most organizations, the recommended practices for password creation involve setting a unique password for all accounts, making sure the password is as random as possible – combining upper- and lower-case letters, numbers and special characters – is at least 8 characters long, and does not contain dictionary words.
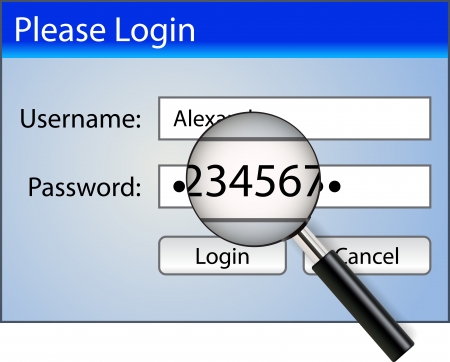
The theory is that, by incorporating a range of character formats and avoiding dictionary words, passwords will be strong enough to resist brute force attacks by cybercriminals attempting to hack login credentials. Cybercriminals use lists of dictionary words and passwords compromised in previous data breaches in brute force attacks, and also employ algorithms that are capable of guessing weak passwords quickly.
Many organizations have adopted password polices with the recommended password complexity requirements; but doing so does not always mean that strong, complex passwords are set by employees. In fact, in many cases, the adoption of arbitrary password complexity requirements does not actually improve the strength of employee passwords.
Complex passwords are required to resist brute force attacks, but complex passwords are also difficult for people to remember. What tends to happen in practice is passwords are created that meet the minimum complexity requirements, but they are still incredibly weak.
Users will take security shortcuts when creating passwords so they can more easily remember their passwords. An extreme example would be “Password123!,” which satisfies the requirement for upper- and lower-case letters, numbers, and special characters, but could be cracked by an algorithm in a fraction of a second. This may be an extreme example, but employees often create passwords that are weak regardless of password complexity requirements.
It is also common for certain letters, numbers and special characters to be substituted. It is very common to replace an l with an exclamation mark, an E with a 3, or an S with a 5. These changes make no difference to the strength of a password. They only give users a false sense of security.
The National Institute of Standards and Technology (NIST) recently updated its password guidance for this very reason and advised against the use of special characters as they did little, in practice, to improve password strength. NIST’s key change in its recommendations was to increase the maximum password length to 64 characters to encourage the use of passphrases rather than passwords. The logic behind the updated advice is that increased length results in increased complexity, but passphrases are also easy to remember.
UK National Cyber Security Centre Recommends Using Three Random Words for Passwords
Last week, the UK National Cyber Security Centre (NCSC), part of the Government Communications Headquarters (GCHQ), recommend a new approach for password creation that goes some way towards resolving the issue of password complexity while also improving usability.
“Counterintuitively, the enforcement of these complexity requirements results in the creation of more predictable passwords,” explained NCSC. “Security that’s not usable doesn’t work.” The approach recommended by NCSC is in a similar vein to that of NIST in that it encourages the use of a passphrase, but makes the creation of that passphrase very simple. NCSC recommends creating a password using three random words.
The logic behind this approach is that traditional password advice built around password complexity has failed to actually improve the strength of passwords. It is not practical as most people cannot remember complex passwords. The creation of passwords from a string of three random words is sufficiently complex for most uses, but the passwords are more user friendly as they can be easily remembered.
Passwords consisting of 3 random words will generally be longer than the recommended minimum of 8 characters, and those words will be created in a way that does not rely on predictable patterns. The approach is also quick to explain and easy to follow. Most passwords include a dictionary word with predictable character replacements, whereas this approach encourages a range of words that may not previously have been considered. It also greatly improves usability as substantial effort is not required, so there is less chance of individuals re-using old passwords or subtly changing them when a password change is required.
This is Not a Password Panacea
NCSC points out that its recommendations are not a password panacea, and may not be appropriate for all organizations, especially those that are already using good strategies for creating strong, unique passwords. That said, the logic is sound, and it could improve password strength for many organizations and individuals.
While some password cracking algorithms have been developed that are optimized for three random words, attackers are unlikely to know that an organization as adopted this approach, which means hackers would need to use multiple algorithms, which is harder and takes longer than just using one.
There may be combinations of three words that feature on commonly used password lists – letmein for example. Organizations should therefore still continue to prohibit these passwords and should encourage users to opt for longer and less predictable words.
“To make it harder for attackers, we need to increase the diversity of password use,” explained NCSC. “This means reducing the number of passwords that are discoverable by cheap and efficient search algorithms, forcing an attacker to run multiple search algorithms (or use inefficient algorithms) to recover a useful number of passwords.”
One issue the three random word approach does not solve is having to create and remember unique passphrases for multiple accounts. The solution is to therefore use a password manager such as Bitwarden.
A password manager is the most secure solution for creating and storing passwords, especially if users take advantage of the random password generator included in these solutions. A very strong, random, complex password can be set for all accounts, which will be at least as strong as passphrases and any human generated password. The three random word approach can then be used for the master password that users have to set to access their password vault.
Unfortunately, “there is still a very low uptake of password managers,” explained NCSC in a recent blog post. “We hope more people will adopt password managers and this will also increase the diversity of passwords.”